|
| 1 | +--- |
| 2 | +title: "Forward-auth, Another Choice for Authentication Function" |
| 3 | +authors: |
| 4 | + - name: "Zeping Bai" |
| 5 | + title: "Author" |
| 6 | + url: "https://github.com/bzp2010" |
| 7 | + image_url: "https://avatars.githubusercontent.com/u/8078418?v=4" |
| 8 | + - name: "Sylvia" |
| 9 | + title: "Technical Writer" |
| 10 | + url: "https://github.com/SylviaBABY" |
| 11 | + image_url: "https://avatars.githubusercontent.com/u/39793568?v=4" |
| 12 | +keywords: |
| 13 | +- Apache APISIX |
| 14 | +- Authentication |
| 15 | +- Plugin |
| 16 | +- Ecosystem |
| 17 | +description: This article describes the use of `forward-auth`, a new plugin in Apache APISIX, and provides detailed instructions on how to use this cleanly designed authentication model. |
| 18 | +tags: [Technology,Ecosystem,Authentication] |
| 19 | +--- |
| 20 | + |
| 21 | +> This article describes the use of `forward-auth`, a new plugin in Apache APISIX, and provides detailed instructions on how to use this cleanly designed authentication model. |
| 22 | +
|
| 23 | +<!--truncate--> |
| 24 | + |
| 25 | +Forward Auth cleverly moves the authentication and authorization logic to a dedicated external service, where the gateway forwards the user's request to the authentication service and blocks the original request and replaces the result when the authentication service responds with a non-20x status. In this way, it is possible to return a custom error or redirect the user to the authentication page if the authentication fails. |
| 26 | + |
| 27 | +## Principle |
| 28 | + |
| 29 | +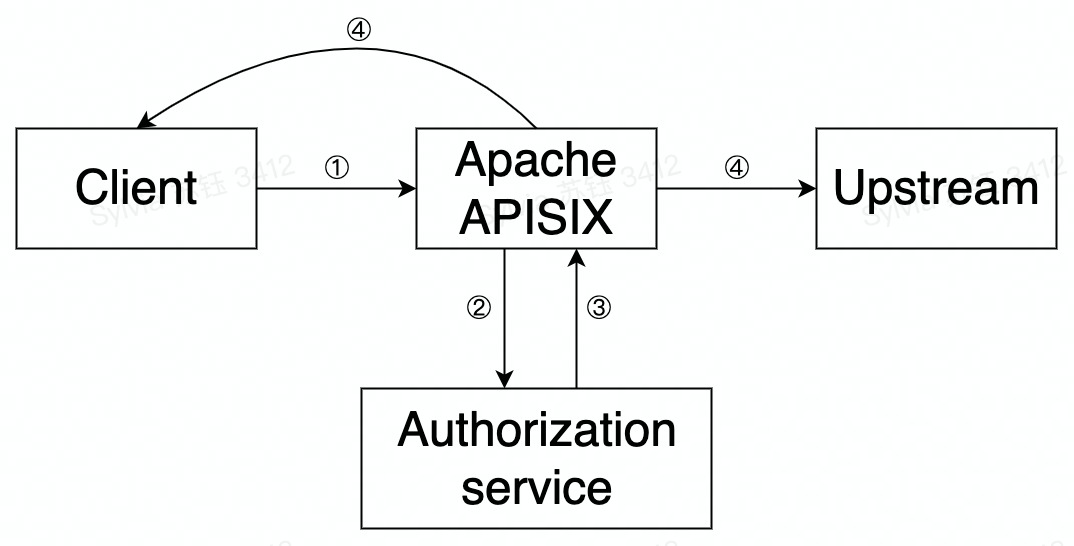 |
| 30 | + |
| 31 | +The principle and flow of the `forward-auth plugin` in Apache APISIX is shown in the figure above and is summarized in the following steps. |
| 32 | + |
| 33 | +- Step 1: A request is made by the client to APISIX |
| 34 | +- Step 2: APISIX makes a request to the user-configured authentication service |
| 35 | +- Step 3: The authentication service responds (2xx or exception status) |
| 36 | +- Step 4: Based on the authentication service response, APISIX will decide to forward the request upstream or send a rejection response directly to the client |
| 37 | + |
| 38 | +## How to use |
| 39 | + |
| 40 | +### Step 1: Set up the authentication service |
| 41 | + |
| 42 | +Suppose there is an authentication service to which the user sends a request with an Authorization request header. If this data passes authentication, a 200 status code and a response header named `X-User-ID` are returned; if it does not pass authentication, the authentication status is considered expired and a 302 status code and `Location` response header are returned to redirect the client to the login page. |
| 43 | + |
| 44 | +### Step 2: Create a route and enable the `forward-auth` plugin |
| 45 | + |
| 46 | +Next, we will configure a route and enable the `forward-auth` plugin to interface the above authentication service with the upstream application. |
| 47 | + |
| 48 | +```shell |
| 49 | +curl http://127.0.0.1:9080/apisix/admin/routes/1 -H 'X-API-KEY: edd1c9f034335f136f87ad84b625c8f1' -X PUT -d ' |
| 50 | +{ |
| 51 | + "plugins": { |
| 52 | + "forward-auth": { |
| 53 | + "address": "http://127.0.0.1:9080/auth", |
| 54 | + "request_headers": ["Authorization"], |
| 55 | + "upstream_headers": ["X-User-ID"], |
| 56 | + "client_headers": ["Location"] |
| 57 | + } |
| 58 | + }, |
| 59 | + "uri": "/user" |
| 60 | +}' |
| 61 | +``` |
| 62 | + |
| 63 | +The above configuration details are explained. |
| 64 | + |
| 65 | +- When a request matches the current route, a request is sent to the `address` in address with the request header Authorization defined in `request_headers` (i.e., the request header configured to be forwarded by the client to the authentication service, if not set, no request header is forwarded), whereby the authentication service can confirm the user's identity. |
| 66 | +- If the authentication passes, the status code is 200 and returns an `X-User-ID` as defined in `upstream_headers` (i.e. the request header to be forwarded upstream by the authentication service when the authentication passes, if not set, no request header is forwarded). |
| 67 | +- If authentication fails, the status code is 302 and returns a `Location` as defined in `client_headers` (i.e., the response header sent by the authentication service to the client if authentication fails, or no response header if it is not set). |
| 68 | + |
| 69 | +### Step 3: Test Requests |
| 70 | + |
| 71 | +```shell |
| 72 | +# Request and send data using POST |
| 73 | +curl http://127.0.0.1:9080/user \ |
| 74 | + --header 'Authorization: true' |
| 75 | + |
| 76 | +HTTP/1.1 200 OK |
| 77 | +Content-Type: application/json |
| 78 | +Content-Length: 28 |
| 79 | +Server: APISIX/2.11.0 |
| 80 | + |
| 81 | +{"user_id":"i-am-real-user"} |
| 82 | + |
| 83 | +# Request using GET |
| 84 | +curl -i http://127.0.0.1:9080/user \ |
| 85 | + --header 'Authorization: false' |
| 86 | + |
| 87 | +HTTP/1.1 302 FOUND |
| 88 | +Server: APISIX/2.11.0 |
| 89 | +Location: https://example.com/auth |
| 90 | +``` |
| 91 | + |
| 92 | +### Addendum: Disable the plugin |
| 93 | + |
| 94 | +If you have finished using the Forward Auth plugin, simply remove the `forward-auth` plugin configuration from the route configuration and save it to turn off the Forward Auth plugin on the route. |
| 95 | + |
| 96 | +Thanks to the dynamic nature of Apache APISIX, there is no need to restart Apache APISIX to turn the plugin on and off. |
| 97 | + |
| 98 | +## Summary |
| 99 | + |
| 100 | +To get more information about the `forward-auth` plugin description and full configuration list, you can refer to the [official documentation](https://apisix.apache.org/docs/apisix/next/plugins/forward-auth). Also, if you have more complex authentication or authorization application scenarios, try using the `opa` plugin, which allows for more powerful functionality in a programmable way. |
| 101 | + |
| 102 | +Apache APISIX is also currently working on additional plugins to support the integration of additional services, so if you are interested, feel free to start a discussion in [GitHub Discussion](https://github.com/apache/apisix/discussions), or via the [mailing list]( https://apisix.apache.org/zh/docs/general/subscribe-guide) to communicate. |
0 commit comments