Replies: 13 comments 4 replies
-
|
Additionally, branch protection is not good enough. If you grant me write access to a repo, I can create my own branch modify the workflow file then run the workflow using my branch. |
Beta Was this translation helpful? Give feedback.
-
|
I'm running in to this issue as well. |
Beta Was this translation helpful? Give feedback.
-
|
@franpb90 and @ecs-jnguyen
Should that work? I have not tested it yet. I was otherwise looking at the CODEOWNERS file but it seems you can still update the file in your feature branch, you just cannot merge it without a code owner review, and thus do not solve the original problem. However, I cannot think of a way to provide write access to the whole repo BUT the github workflow folder, blocking pushes even if on feature branches... |
Beta Was this translation helpful? Give feedback.
-
|
A colleague mentioned a great idea: triggering a workflow through issues. Probably not the perfect solution, but it should solve the issue of triggering a workflow for READ only users that @franpb90 mentioned. |
Beta Was this translation helpful? Give feedback.
-
|
It is wanted as mentioned in etcd-io/etcd#15659. @franpb90 and @gusmith-ambiata could you please share how it is set up? |
Beta Was this translation helpful? Give feedback.
-
|
A somewhat convoluted solution I'm going to try the last piece of. The actual environment we want to deploy to is in Azure, and we are using OIDC in the workflow. Each Azure environment has a separate federated managed identity to the github environment. We needed an action run in a separate job to find the environment for a branch, and to use the output of that job to set the environment for a workflow in a second job. This action enumerates the environments to create a mapping of branch name patterns to github env. If the current branch matches exactly one environment, then that is the environment selected. That second job then uses OIDC to login to Azure, where the identity federation authenticates the github environment's identity. This action runs a simple python script that calls GH API to collect this info, It seems like we will be able, in that action, to fail if the workflow was triggered by an actor that is not one of the CODEOWNERS. The basic issue there are users with write access to the repo that effectively do not have write access to specific branches based on branch protection rules, but the github workflows has no mechanism to determine whether the triggerer has write access to the branch. |
Beta Was this translation helpful? Give feedback.
-
|
+1 |
Beta Was this translation helpful? Give feedback.
-
|
This is required for both of these events, IMO:
The latter one is particularly silly. The endpoint is designed to:
Processes that happen outside of GitHub should not be given any more than the permissions they explicitly need, and certainly not permission to write repository contents. These two dispatch events could be very useful for providing a limited external interface for your CI/CD automation infrastructure. But the current design does not follow the principle of least privilege, which means that developers are forced into hacky solutions like using issues or using branch protection rules to try to close the holes that these permissions open. Fixing this issue would also enable developers to use https://github.com/peter-evans/repository-dispatch (or similar actions) to dispatch an event in another repository using a limited token that properly follows the least-privilege principle. +1 for the idea of an |
Beta Was this translation helpful? Give feedback.
-
|
+1 This is an important security feature |
Beta Was this translation helpful? Give feedback.
-
|
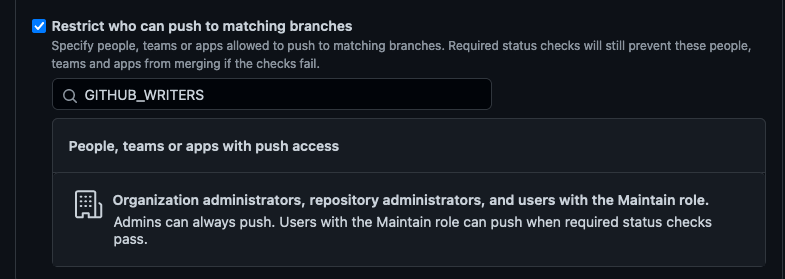
My team uses Rulesets to control which people have full write permissions and which people should only be able to run workflows. Therefore, we created a Ruleset which restricts the creation, updates and deletions of branches. Only repository admins are allowed to bypass these restrictions. Thus, people with write permission can run workflows but cannot create new or update existing branches. You could also add other teams or roles to the bypass list to realise a different behaviour. One advantage compared to the issue approach described above: in case your workflow requires input arguments, you don't have to implement extra logic to extract the data from the issue description. Instead you can use the default dispatch dialog from GitHub. This reduces error potential and complexity. Like the other approaches described before this isn't an ideal solution and there are probably edge cases which my team hasn't noticed so far (In case you see some, please let me know). However, it works for our use cases. |
Beta Was this translation helpful? Give feedback.
-
|
+1 |
Beta Was this translation helpful? Give feedback.
-
|
+1 |
Beta Was this translation helpful? Give feedback.
-
|
I agree with this. Triggering a There are many real cases where teams need controlled execution without code-changing privileges. For example, if a team manages a public-facing service such as a SASSA status check platform, certain staff may need to run deployment, sync, or reporting workflows on demand, while still having no ability to edit workflows, expose secrets, or bypass protections. The same applies to admin tools related to SASSA pensions, where operational access and repository write access should clearly remain separate. So the request makes sense from both a security and operations perspective: read, write, and execute should be treated as distinct permissions, not bundled together. |
Beta Was this translation helpful? Give feedback.



Uh oh!
There was an error while loading. Please reload this page.
Uh oh!
There was an error while loading. Please reload this page.
-
Select Topic Area
Product Feedback
Body
From my understanding to trigger a workflow_dispatch you need to have write permissions on the repository.
We are facing the following situation. We have an internal repository in an organization where all organization members have read access. We want to give them access just to trigger the workflow on a specific branch. We do not want that they can modify the workflows and be able to expose the secrets, take advantage of the privileges configured in the repo, or skip any workflow validation.
In my opinion, running workflows permission should have it's own permission, instead of using the repository write permission. I think it will help to have this permission separated from write permissions, similar like in file permissions we have read, write, and execute
Related discussion:
Who has permission to workflow_dispatch
Beta Was this translation helpful? Give feedback.
All reactions